As we navigate the digital landscape of the 21st century, the public cloud has emerged as a dominant force, revolutionizing the way organizations manage their data and applications. However, this technological advancement has also given rise to unprecedented cyber threats and security challenges. In this comprehensive blog, we will explore cutting-edge solutions that fortify public cloud security, safeguarding sensitive information from malicious actors. Let’s delve into the realm of public cloud security and equip ourselves with the knowledge to protect our digital assets.
Understanding the Public Cloud Landscape
Before we dive into the security measures, let’s grasp the essence of the public cloud. In simple terms, a public cloud is a shared infrastructure hosted and maintained by a third-party cloud service provider. It allows businesses and individuals to store and access data and applications remotely over the internet. Major players in the public cloud space include Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP).
The Gravity of Cyber Threats
With the increasing reliance on the public cloud, cyber threats have grown in scale and sophistication. These threats come in various forms, such as data breaches, DDoS attacks, malware, and insider threats. Cybercriminals target vulnerabilities in the cloud infrastructure and exploit misconfigurations, making robust security measures imperative.
Ensuring Data Encryption and Privacy
Data encryption is a fundamental aspect of cloud security. By encrypting data both at rest and in transit, organizations can ensure that even if attackers gain unauthorized access, the data remains indecipherable. Additionally, implementing access controls and employing multi-factor authentication (MFA) further fortifies data privacy.
Leveraging Zero Trust Architecture
Zero Trust Architecture (ZTA) has gained traction in recent years as an effective security model. It operates under the principle of “never trust, always verify.” ZTA assumes that every user or device trying to access the public cloud is untrusted until proven otherwise. By continuously verifying identities and authorizations, ZTA minimizes the attack surface and enhances security.
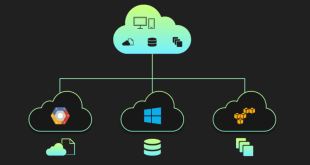
Multi-Cloud Security Strategies
Many organizations adopt a multi-cloud approach, leveraging multiple cloud service providers simultaneously. While this strategy offers flexibility and redundancy, it also introduces security challenges. Implementing a cohesive security framework across various cloud platforms is crucial to mitigating risks and streamlining security management.
Container Security
Containers have become a popular method for packaging and deploying applications in the cloud environment. However, they can introduce security vulnerabilities if not managed properly. Container security solutions, such as vulnerability scanning and runtime monitoring, are vital for identifying and addressing potential risks.
Cloud-Native Security Solutions
Cloud-native security tools are specifically designed to protect cloud-based applications and resources. These solutions offer real-time threat detection, automated incident response, and enhanced visibility into cloud environments. Integrating cloud-native security tools into the workflow strengthens the overall security posture.
Continuous Security Monitoring
In the ever-evolving landscape of cyber threats, continuous security monitoring is essential. Automated monitoring systems that detect anomalies and suspicious activities in real-time can help organizations respond swiftly to potential breaches and minimize the impact.
The Role of Artificial Intelligence (AI)
AI-powered security solutions are increasingly prevalent in the cloud security domain. AI algorithms can analyze vast amounts of data and identify patterns indicative of potential threats. By utilizing AI-driven threat detection, organizations can stay ahead of cybercriminals and predict and prevent security breaches.
Public Cloud Compliance and Auditing
Regulatory compliance is a crucial consideration when migrating to the public cloud. Organizations must adhere to industry-specific regulations and conduct regular security audits to assess their cloud infrastructure’s compliance with established standards.
Final Words
The public cloud is undoubtedly a game-changer, offering unparalleled scalability and efficiency. However, the rise of cyber threats necessitates a proactive and multi-faceted security approach. By leveraging encryption, adopting Zero Trust Architecture, and employing cloud-native security solutions, organizations can safeguard their data and applications from evolving cyber threats.
Commonly Asked Questions
Q1: What is the primary advantage of using a public cloud?
A1: The primary advantage of a public cloud is its scalability, allowing businesses to dynamically adjust resources based on demand without significant upfront investments.
Q2: Is the public cloud secure enough for sensitive data?
A2: Yes, with proper security measures, the public cloud can be secure for sensitive data. Encryption, access controls, and monitoring play a vital role in enhancing security.
Q3: Can AI detect and prevent all cyber threats in the public cloud?
A3: While AI is a powerful tool, no solution can guarantee 100% protection. AI enhances threat detection but should be complemented with other security measures.
Q4: How can organizations ensure compliance in the public cloud?
A4: Organizations must align their cloud infrastructure with industry-specific regulations, conduct regular audits, and implement appropriate security controls.
Q5: Are there any disadvantages to a multi-cloud strategy?
A5: While multi-cloud offers benefits, it can also increase complexity in management and security. Organizations need proper planning to mitigate potential downsides.
 webfily
webfily