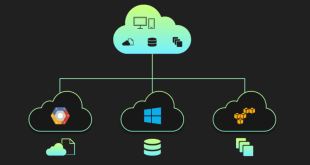
In the fast-paced digital landscape of the post-2021 era, where businesses heavily rely on cloud computing, securing multi-cloud deployments has become a paramount concern. The rise of hybrid cloud solutions has unlocked significant synergy in multi-cloud strategies, but it has also introduced new challenges for cybersecurity. This comprehensive blog explores the concept of Zero Trust Security and how it can fortify your organization’s multi-cloud environments against ever-evolving threats.
Understanding Zero Trust Security
Zero Trust Security is a proactive cybersecurity approach that assumes no implicit trust for any user or device, whether inside or outside the network perimeter. In other words, it treats every access request as potentially malicious, even if it originates from within the organization’s network. The fundamental principle is to verify every access attempt before granting entry, reducing the risk of unauthorized access or data breaches.
The concept of Zero Trust Security was first introduced by Forrester Research in 2010, but it has gained immense popularity and adoption in recent years due to the increasing sophistication of cyber threats.
The Core Tenets of Zero Trust Security
Micro-Segmentation
Micro-segmentation involves dividing the network into smaller, isolated segments or zones. Each segment contains specific resources with distinct access controls. This approach limits the lateral movement of attackers within the network, significantly reducing the impact of potential breaches.
Least Privilege Access
Zero Trust Security follows the principle of granting the least privilege necessary for users and devices to perform their tasks. By minimizing unnecessary access rights, the attack surface diminishes, making it harder for malicious actors to exploit vulnerabilities.
Continuous Authentication
Traditional perimeter-based security relies on a one-time authentication process. In contrast, Zero Trust Security employs continuous authentication to monitor user behavior and device health throughout a session. This dynamic approach enhances security by detecting and preventing anomalous activities promptly.
Implementing Zero Trust in Multi-Cloud Deployments
With organizations increasingly adopting multi-cloud strategies to leverage the strengths of different cloud providers, securing these complex environments becomes critical. Here’s how Zero Trust Security can be applied to multi-cloud deployments:
Identity and Access Management (IAM)
IAM plays a pivotal role in a Zero Trust Security model. Adopting robust IAM practices across all cloud platforms ensures that only authorized users with valid credentials can access resources. It involves the use of strong authentication methods, like multi-factor authentication (MFA), to enhance identity verification.
Network Segmentation and Isolation
Just as micro-segmentation enhances security within a single cloud network, isolating different cloud environments from each other is essential in multi-cloud deployments. By segmenting networks and applying access controls, the risk of lateral movement between clouds is minimized.
Encryption and Data Protection
Encrypting data at rest and in transit is a crucial aspect of Zero Trust Security. This measure safeguards sensitive information from unauthorized access, even if an attacker manages to breach other layers of security.
Challenges and Considerations
Complexity and Integration
Implementing Zero Trust Security in multi-cloud environments can be complex, especially when dealing with various cloud providers and existing security tools. It requires careful planning, coordination, and integration to ensure seamless operation.
User Experience
While stringent security measures are necessary, they should not hinder the user experience. Striking the right balance between security and user convenience is essential to ensure smooth operations and high productivity.
Constant Adaptation
Cyber threats evolve continuously, demanding constant adaptation of Zero Trust Security measures. Organizations need to stay vigilant, update policies, and adopt emerging security technologies to stay ahead of potential risks.
Final Words
In the post-2021 era, where cyber threats are more sophisticated than ever, Zero Trust Security offers a robust approach to safeguarding multi-cloud deployments. By treating every access request as potentially malicious and continuously verifying users and devices, organizations can significantly enhance their security posture in the dynamic world of cloud computing.
Commonly Asked Questions
Q1: Can Zero Trust Security be implemented in a traditional on-premises environment?
Yes, Zero Trust Security principles can be applied to both on-premises and cloud-based environments. The core tenets of Zero Trust, such as micro-segmentation and least privilege access, can fortify any network against cyber threats.
Q2: Is Zero Trust Security cost-effective for small businesses?
While implementing Zero Trust Security may require initial investments in infrastructure and training, its long-term benefits in preventing data breaches and mitigating cyber risks make it cost-effective for businesses of all sizes.
Q3: Does Zero Trust Security eliminate the need for traditional firewalls and antivirus software?
Zero Trust Security complements traditional security measures like firewalls and antivirus software but does not replace them entirely. It adds an extra layer of protection by focusing on user behavior and access control.
Q4: Is Zero Trust Security suitable for organizations with a BYOD (Bring Your Own Device) policy?
Yes, Zero Trust Security is well-suited for organizations with a BYOD policy. By continuously authenticating users and monitoring devices’ health, it helps maintain security even with diverse endpoints.
Q5: Can Zero Trust Security be adopted incrementally, or does it require a complete overhaul of existing systems?
Zero Trust Security can be implemented incrementally, allowing organizations to phase in the new approach gradually. This approach allows for smoother integration with existing systems and minimizes disruptions during the transition.
 webfily
webfily