Welcome to our comprehensive guide on the revolutionary concept of confidential computing and its paramount role in securing cloud data beyond traditional encryption methods. In today’s rapidly evolving digital landscape, where data breaches have become all too common, ensuring the utmost security for sensitive information stored in the cloud has become an imperative. In this blog, we delve into the realm of confidential computing, exploring its unique approach, benefits, and how it surpasses conventional security measures. Join us as we unlock the power of confidential computing and empower your cloud data security like never before.
Understanding the Limitations of Traditional Cloud Security
Before we embark on our journey into confidential computing, it is crucial to recognize the limitations of conventional cloud security practices, such as encryption. While encryption plays a significant role in safeguarding data, it has its drawbacks.
- Data Exposure During Processing: Encrypted data becomes vulnerable during computation, as it needs to be decrypted for processing, leaving it susceptible to potential attacks.
- Insider Threats: In traditional cloud environments, insiders with access to decryption keys could misuse or leak sensitive data, posing significant risks.
Enter Confidential Computing: A Paradigm Shift
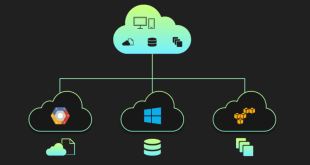
Confidential computing presents a paradigm shift in cloud data security, addressing the vulnerabilities left by encryption. It enables data to remain encrypted even during processing, thereby mitigating risks associated with data exposure.
The Three Pillars of Confidential Computing
Secure Enclaves
Secure enclaves, also known as trusted execution environments, are isolated regions within a processor that protect data during processing. They operate independently of the underlying operating system and hardware, ensuring data confidentiality and integrity.
Confidential Virtual Machines
Confidential virtual machines extend the concept of secure enclaves to cloud-based virtual machines. They allow encryption keys and sensitive data to be held within the secure enclave, providing robust protection against unauthorized access.
Secure Multi-Party Computation (SMPC)
SMPC is a cryptographic technique that enables multiple parties to compute on encrypted data collaboratively. It ensures that individual data remains confidential, and the results of computations are revealed without revealing the underlying data.
The Advantages of Confidential Computing
Confidential computing offers several key advantages, making it a compelling approach to cloud data security:
- Data Privacy During Processing: Confidential computing ensures that sensitive data remains encrypted during computation, minimizing the risk of exposure.
- Enhanced Insider Threat Protection: By safeguarding data within secure enclaves, confidential computing reduces the impact of insider threats.
- Confidence in Cloud Services: Organizations can confidently adopt cloud services, knowing that their data remains secure and confidential.
Confidential Computing Use Cases
Healthcare and Medical Research
In the healthcare industry, confidential computing allows medical researchers to collaborate securely on encrypted patient data, accelerating research while safeguarding patient privacy.
Financial Services
Financial institutions can leverage confidential computing to process encrypted financial transactions securely, protecting customer data and ensuring compliance with industry regulations.
Machine Learning and AI
Confidential computing facilitates secure, collaborative machine learning models, enabling organizations to share sensitive data for training without compromising privacy.
Implementing Confidential Computing
Implementing confidential computing requires careful planning and collaboration between cloud providers and customers. Key steps include:
- Choosing the Right Cloud Provider: Selecting a provider with robust confidential computing capabilities and industry certifications.
- Identifying Confidential Data: Determining which data requires the highest level of protection and should be processed within secure enclaves.
- Testing and Validation: Rigorous testing and validation of the confidential computing infrastructure to ensure its effectiveness.
Final Words
In a world where data breaches are a constant threat, confidential computing emerges as a game-changing solution to secure cloud data beyond traditional encryption methods. By harnessing the power of secure enclaves, confidential virtual machines, and secure multi-party computation, organizations can fortify their data privacy, protect against insider threats, and confidently leverage cloud services.
Commonly Asked Questions
1. Can confidential computing be combined with traditional encryption methods?
Yes, confidential computing can complement traditional encryption methods, providing an additional layer of protection to sensitive data during processing.
2. Does confidential computing impact performance?
While there may be slight performance overhead due to the computational demands of secure enclaves, advancements in hardware and software optimizations are continuously improving performance.
3. Is confidential computing suitable for all types of data?
Confidential computing is particularly valuable for highly sensitive data, such as personal and financial information, intellectual property, and proprietary research.
4. Can confidential computing prevent data breaches entirely?
While confidential computing significantly reduces the risk of data breaches, no security measure can guarantee absolute protection. It should be part of a comprehensive security strategy.
5. How do I know if my cloud provider supports confidential computing?
Check with your cloud provider to understand their confidential computing capabilities and ensure they meet your specific security requirements. Many leading providers now offer confidential computing services.
 webfily
webfily